OSINT on Sanctioned Companies: the Askarlab Case by UnderYourNoZ
As some of our readers on social media may know, the EU has recently approved its 15th sanctions package against Russia, aiming to close loopholes that have allowed Moscow to import Western electronics via third countries like Türkiye and Kazakhstan. Taking it from here, how can OSINT craft help you investigate on companies and owners who keep undermining international sanctions? How can we expose them and make sure they’re under the spotlight? Let’s have a look, starting like in our last article (read here) from an excellent piece by The Insider last month on a Kazakh company named LLP Askarlab.
The Insider’s take
The Insider has revealed that “advanced electronic warfare technology” from Western manufacturers is reaching Russia through intermediaries in Kazakhstan, circumventing international sanctions. Kazakh firms, notably Askarlab and Dicosta Technologies, have been importing high-end equipment from companies such as Germany’s Rohde & Schwarz, France’s Safran Data Systems, and U.S.-based Keysight Technologies. This equipment, including oscilloscopes, signal generators, and satellite modems, is essential for developing sophisticated systems used by the Russian military.

The Insider gain access to customs records indicating that these devices are initially imported into Kazakhstan and subsequently re-exported to Russia. For instance, in March 2024, an oscilloscope from Rohde & Schwarz was imported into Almaty and, by April, had been shipped to Moscow’s Sheremetyevo Airport, with the Russian company Infostera LLC listed as the recipient. Similarly, satellite modems from Safran Data Systems were imported into Kazakhstan and later appeared in Russian customs records, with Computer Services Ltd. acting as the exporter.
The Insider’s investigation also involved direct communication with a Kazakhstan-based intermediary, who confirmed the ongoing deliveries to Russia. This clandestine supply chain enables Russia to acquire critical technology for its military applications, effectively bypassing sanctions imposed by Western nations.
Going further through OSINT: UnderYourNoZ followed the lead
While having companies exposed for the wrongdoings matters, we at UnderYourNoZ believe that only people do make changes. Be it for good or bad. In its article, The Inspire mentions the name of one man: the CEO of LLP Askarlab Alexander Lissitsin. So we decided to take it from there to see what could be found with basic OSINT research.
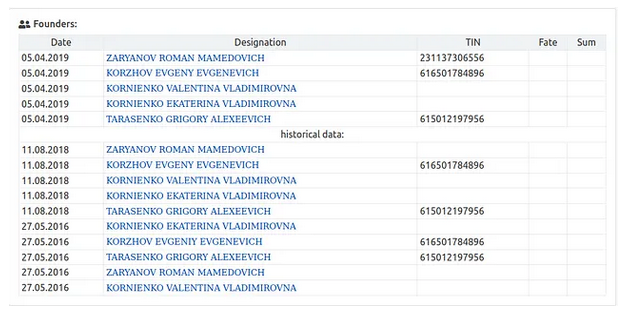
First we wanted to confirm our man’s identity so we went looking for data on his company. Using commercial registers from Kazakhstan like ba.prg.kz, volza.com or www.goszakup.gov.kz. Among the information listed such as the date of registration (29 of July 2016) or the legal address of the company (050000 G. Almaty pr. Dostik, D.128, N.p. 180, Kazakhstan), we found confirmation that “Alexandandri Lisycin” (ЛИСИЦИН АЛЕКСАНДР ПАВЛОВИЧ for the original) is the head of Askarlab.
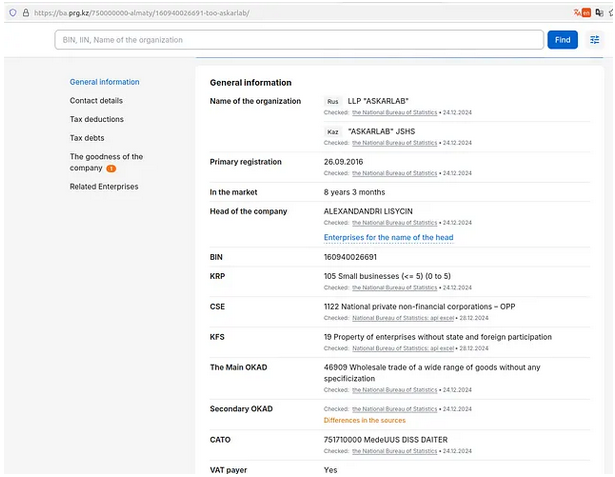
Source: ba.prg.kz
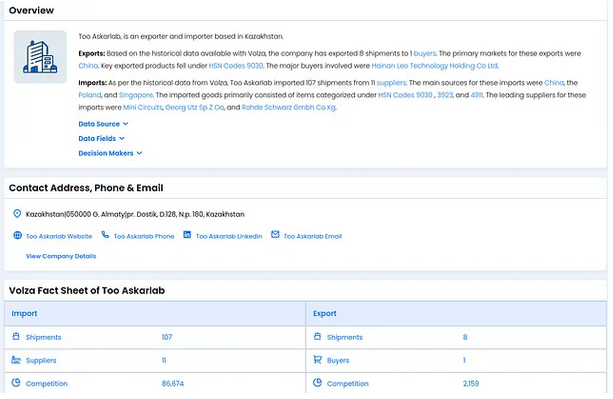
Source: volza.com
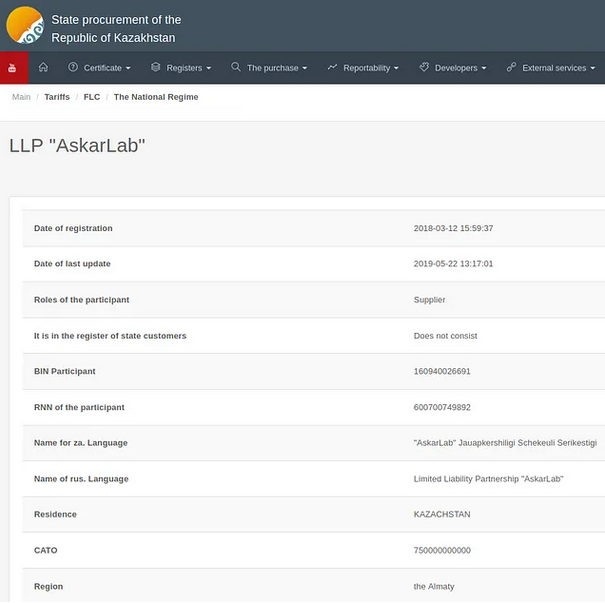
www.goszakup.gov.kz
This highlight an important skill to develop for an OSINT investigator: you need to go for so-called “local” source of information (here Kazakhstan) though you don’t master the language. Many tools can help you with translation nowadays so use it! By the way, it appears that “askar” mean “military”. Coincidence?
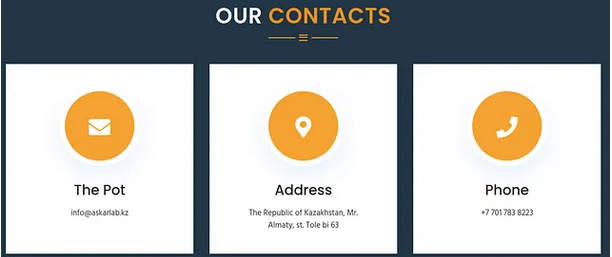
The ba.prg.kz page of the company provided us with two phone numbers +77017838223 and +77017813298. While we didn’t find any social associated with the second one, the first number is indeed associated to a Telegram account that has been recently active.
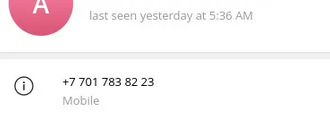
This number can also actually be found on the website of Askarlab. Someone within the company might be using it for professional and personal matters.
We also found a third number on the compliance website http://swis.trade.kg: +79133739874 but it lead to a dead-end.
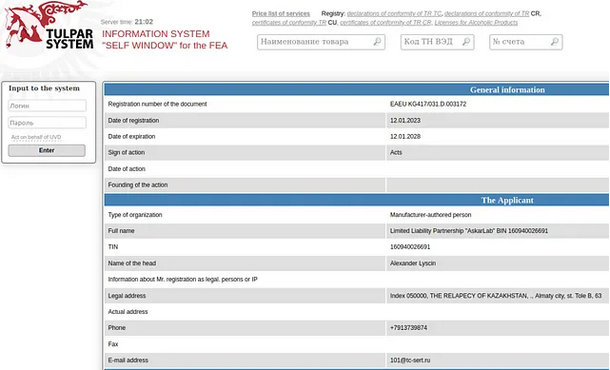
Source: swis.trade.kg
Who really is Alexander Lissitsin?
Having confirmed he was Askarlab’s CEO with OSINT data, we wanted to know more. Using a Google advanced query, we found out a profile created in August 2008 on Xing.com that match (declared location is Almaty where the company is also located). With a sock puppet profile, we came out with something lacking in any article we read so far: a profile photo and some data on his professional career!
Disclaimer: Here a little OPSEC notice on the use of sock puppets to find out information on your targets: be careful to use a completely separate environment from your workspace. Don’t register using personal emails or anything related to your real identity.
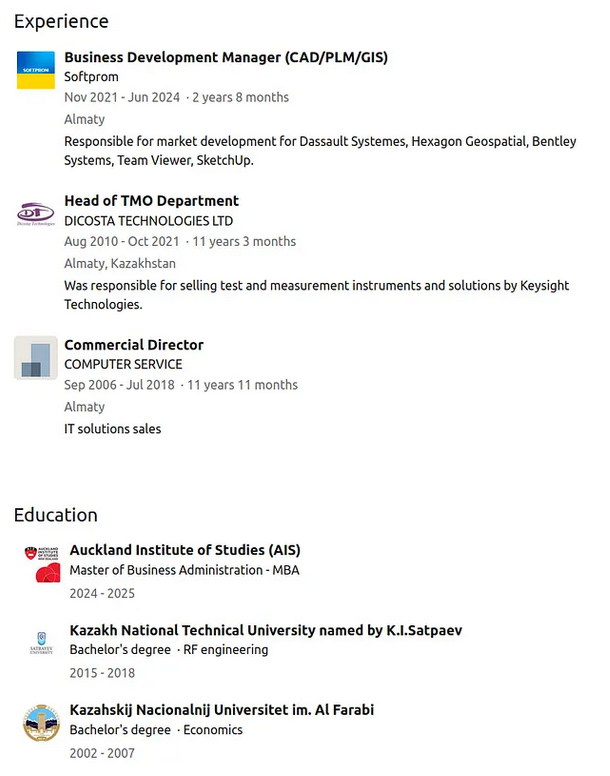
Alexander Lissitsin claims to be an IT specialist and also to have skills in project coordination, finance and sales management. Looks like he forgot to mention sanctions dodging. He’s only link to two people without any further indication that they could be linked to Askarlab’s activities. He listed his activity as account manager in a “Computer Service Ltd” since September 2006 and to have study at the Al-Farabi University from 2002 to 2007. As a hobby, Lissitsin indicated: music, sports and trips.
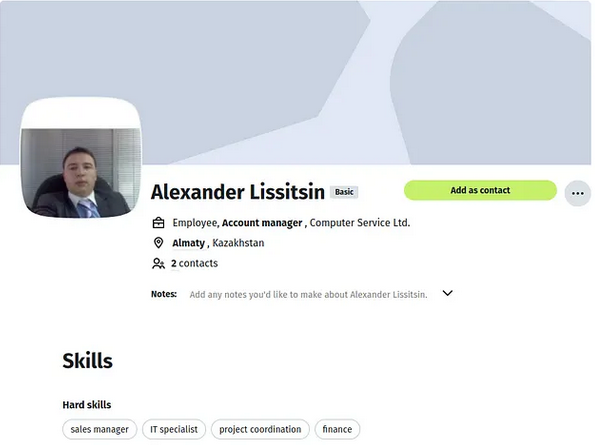
Source: xing.com
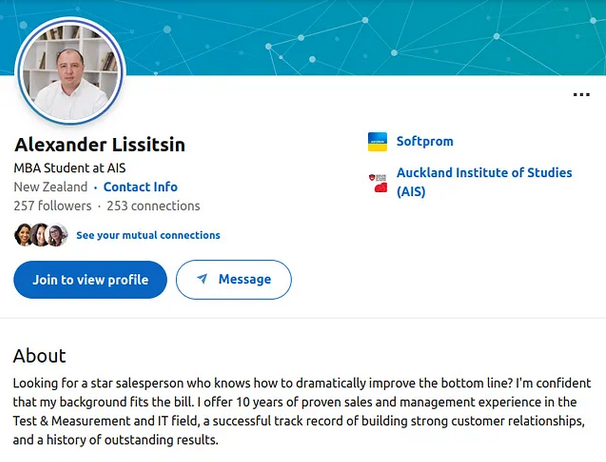
With these details in mind, we managed to identify a LinkedIn account that also matched the identity of Alexander Lissitsin. The profile picture definitely matches though one could tell from his hair that he has aged a bit. The price for supporting Russia’s war effort. On LinkedIn, Lissitsin is listed as a Business Development Manager at Softprom working with some major Western companies from the defense or space industries. As further proof that we had the right guy, he displayed he was head of TMO department at Dicosta Technologies LTD from 2010 to 2011, a company whose involvement in the sanctions dodging scheme was revealed by The Insider. We can also understand further his academic background, knowing he did study at Al-Farabi University where he earned a bachelor’s degree in Economics (dates match the Xing profile) but also has a degree in engineering from the Kazakh National Technical University.
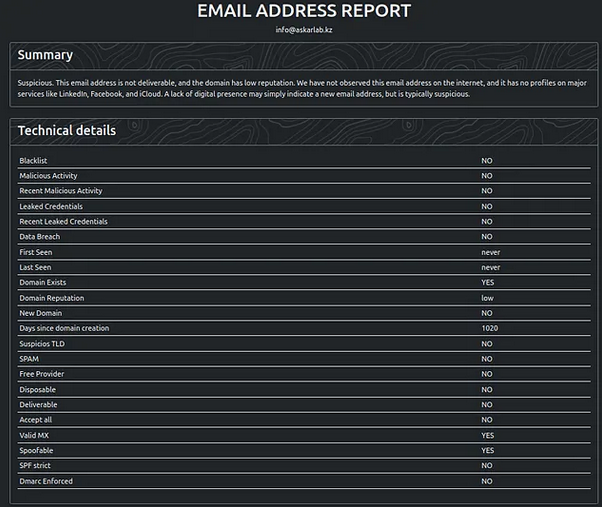
How could one try to have confirmation of his involvement in the dodging scheme? The easiest way would be for any journalist to contact the displayed email on the Askarlab’s website: info@askarlab.com. At UnderYourNoZ, we went a little further and checked it with Synapsint to see whether or not we couldn’t find any mention of the mail address in leaked data but no result came out this time. No more pivoting here.
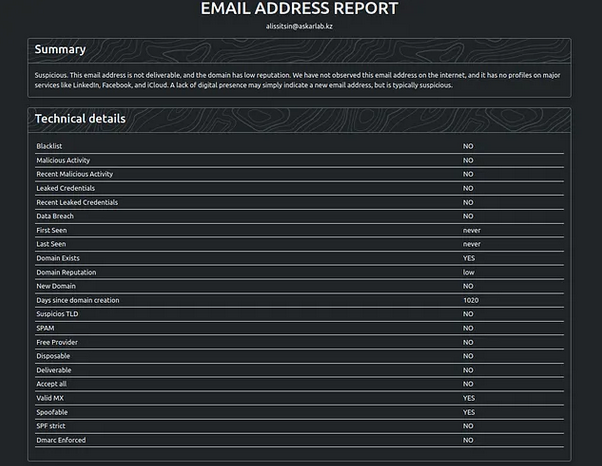
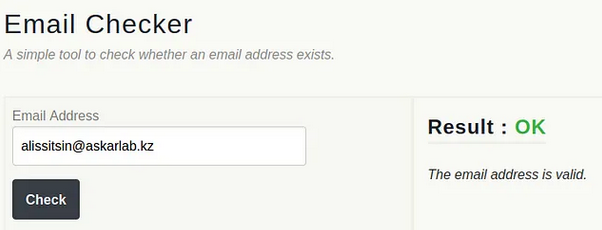
But we look out for more. In a side article (read it here) on Askarlab, Orda disclosed an email linked to Discosta Technologies (mentioned in The Insider’s piece) that ringed a bell: alissitsin@dicosta.kz. “alissitsin” can easily be identified for “Alexander Lissitsin”, especially that we do know he worked for Dicosta. From there we gave it a try: did the mail address alissitsin@askarlab.kz exist? It apparently does so here’s another way to try to have some answers from our man.
What’s next?
A starting point, a few OSINT tools and a lot of curiosity is just what it took UnderYourNoZ to know a lot more about someone directly involved in Russia’s effort to keep the war ragging on European soil. We surely missed a lot and it’s up to you to keep on and hunt for more. Everyone has the power not to remain silent and help with some simple skill sets and some time.
Join the UnderYourNoZ journey by reading and sharing our articles on social media. Do not hesitate to reach out for anonymous tips at underyournoz@protonmail.com. We guarantee that we’ll into look into it.
Update: Further investigation led by our mate OSINT Ambition (follow him here and subscribe to his newsletter here) helped identify that the phone number +77017813298 is linked to a Skype account displaying the name Камила Якубова (Kamila Yakubova). As for the phone number +77017838223, the name Лисицын Александр (Lissitsyn Alexander) is displayed in Truecaller, a well-known caller identification app, confirming it belongs to the CEO of Askarlab.
Table of contents
> The Insider's take
> Going further with OSINT
> Who really is Alexander Lissitsin?
> What's next?